Edition 11 – One mistake ties together more than 100 domains
Hey there,
Hakan here. This week's edition is going to be a short one about mistakes. Without those, it'd be a whole lot harder to do my job. When trying to find out who hackers are – or in this case, people running information operations – you need to find a thread you can pull on. Here's one way to do it.
Doppelgänger

Through a source, I was able to get forensic copies of websites controlled by Doppelgänger. By that I mean everything an admin would see after logging in – e.g. certificates, site statistics, logs, pictures uploaded etc.. To be absolutely clear: I didn't log in, I was provided with a frozen copy of a site that had been live.
If you think, keys, certificates and other items could be of relevance to your investigations, feel free to reach out: readwritenewsletter@proton.me
And by Doppelgänger I mean the information operation that is pushing Kremlin-friendly narratives. That's the short version of it. If you would rather read the book version, here's an 277-page affidavit by the F.B.I.
One part of Doppelgänger's operation is running on Wordpress. At first, I didn't think there would be anything to report on. Mostly because there's already a lot of very good reporting out there (see the sources-section here). The stuff I had access to was interesting, but more to me than to a wider audience.
To give you one example, I had access to the logs, i.e what IP addresses visited those disinformation websites. Turns out, in a five-day period the ChatGPT-bot visited one of the sites more than 700 times. That's an interesting data point – if those LLMs were to incorporate that body of text into their accepted version of "reality", it could be a problem – but the data I had lacked context. Meaning, it's also very likely (more so, even!) that ChatGPT was pointed to a website and deemed the content to be false.

While perusing through some of the sites, I came across a weirdly formatted string in one of the HTML sites. This absolutely is a freak find, and all I had was a gut feeling that something felt somehow off. Off like: "I wonder whether this is not part of the standard configuration of whatever this plugin is doing and a human person might've edited this?"
The plugin in question is called Ajax load more and it's main purpose is to lazy load websites while infinite-scrolling. I had no idea about this plugin prior to this, I just thought: What's up with those numbers in 9317641231_vars?

Enter Urlscan
Urlscan is a website that allows you to, well, scan URLs. It will pay them a visit and store everything it can load and make it searchable afterwards: the entire DOM, all of the redirects, the javascript, and so on. I use Urlscan quite regularly, because some of the features can be extremely helpful, to name one: the screenshots taken when visiting those domains.
Urlscan also has a pro-version to which Johannes Gilger, the CEO, was kind enough to give me access to a while back. In the pro-version, you can search for strings directly. Which is what I did. Turns out, there are a lot of results.
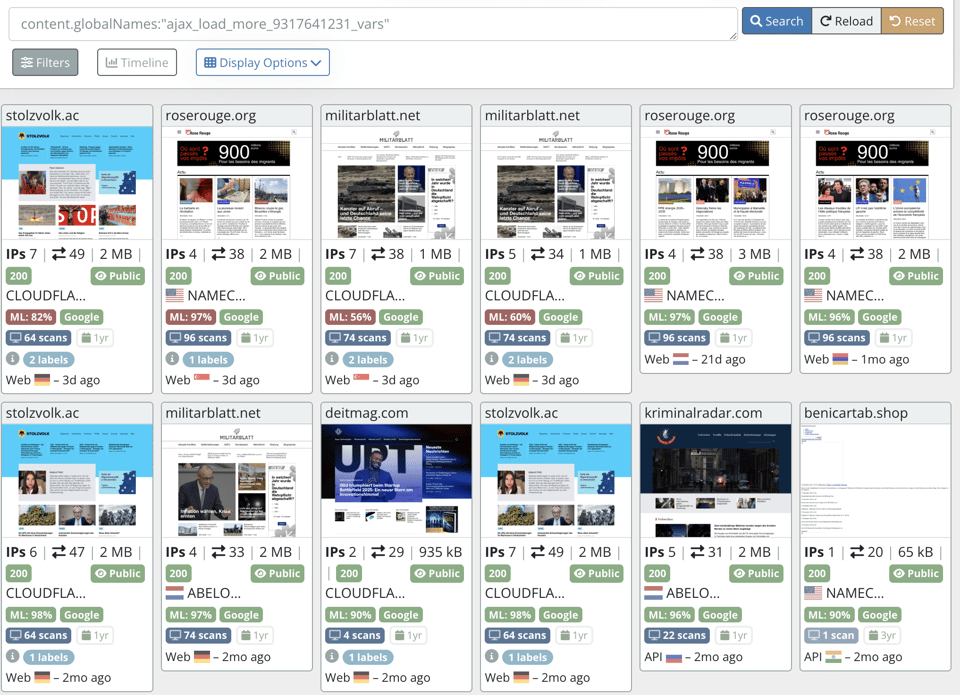
Just by eyeballing the domain names I am fairly certain that these domains are connected to the Doppelgänger campaign. However, I didn't check all of the domains, so some further corroborating is needed. For many domains, a quick google search will lead you to this CISA report (PDF) from 2024. Here's the full list of domains tied to 9317641231_vars.
Right around then, during my day job, I met "Hugo" – and Hugo told me that he had hacked huge parts of the Doppelgänger infrastructure. We've published a story about him at Der Spiegel and ZDF.
Thanks for reading and talk soon!