May 3, 2026
May 3, 2026
The RansomISAC published regarding "Zhengzhou 403 Network Technology Co., Ltd.", a cert we reported in 2025 after it was used to sign CobaltStrike. Their investigation seemed like a wild adventure, check it out. https://t.co/l29WFGyMqP
— Squiblydoo (@SquiblydooBlog) May 3, 2026
1/3

DragonBreath: Dragon in the Kernel | Ransom-ISAC Blog - Ransom-ISAC
A 0-day BYOVD vulnerability in dragoncore_k.sys signed by Zhengzhou 403 Network Technology, with shell company analysis, Dragon Breath APT-Q-27 attribution, and an APT31 / Wuhan Xiaoruizhi personnel nexus.
It's been almost 2 years since the joint work between @GoogleDeepMind and @Google Project Zero demonstrated the vulnerability finding capabilities of these new LLMs. We saw that the pace & volume of vulnerability discovery would grow rapidly in the following quarters and years🧵
— Royal Hansen (@royalhansen) May 3, 2026
Google VRP modifications are the result of AI changing the economics of software security in real time. This trend will only accelerate over the next ~12 months. This should not be surprising at all if you've been paying attention to the capability curve.https://t.co/GUX5zIdeGQ
— chrisrohlf (@chrisrohlf) May 1, 2026

Blog: Evolving the Android & Chrome VRPs for the AI Era
We are announcing changes to the Chrome & Android Vulnerability Reward Programs (VRP) which take effect immediately and are focused on adjusting our reward amounts and bonuses to reflect the types of reports and bug categories that provide the most value to security today.
Human in the loop has strong "don't click on untrusted links" vibes..
— Claudio Criscione (@paradoxengine) May 1, 2026
hot take: dropping an advisory on unpatched $THING is appropriate under some circumstances, and timeline expiry is one of them
— cje (@caseyjohnellis) May 3, 2026
where @taviso gets invoked a lot still is that new players look at the end state (the published advisory) and speed-run that part without understanding…
https://as.ft.com/r/33f7fc2c-39d3-4d92-9be7-1d2d3d26c5b9This is such a brilliant piece by Chris Miller, the FT's Ukraine correspondent on the incredible fortitude of a drone commander on the eastern front - please read it. https://t.co/gz1I0Bp66e
— Cordelia Jenkins (@CordeliaJ) May 2, 2026
Ghost Operators: How Israeli Telecoms Were Exploited to Track Citizens Worldwide https://t.co/aFpP3qGCLi
— profdeibert (@RonDeibert) May 3, 2026

Ghost Operators: How Israeli Telecoms Were Exploited to Track Citizens Worldwide - National Security & Cyber
Report Shows How an SMS Exploit Turns Smartphones Into Tracking Devices – and How 4G and 5G Networks Are Abused
https://littlelailo.github.io/writeups/coruna.htmlHad a lot of fun reversing Coruna over the last couple weeks and decided it would be worth to write it all up before I forget - so enjoy :)https://t.co/DWld4SWgf6
— littlelailo (@littlelailo) May 2, 2026
I'm now unemployed. I hear that the oss community is buried in AI bug reports and don't have enough people to triage and verify. Where is the sign up sheet?
— Paul Vixie (@paulvixie) May 2, 2026
New Google VRP writeup "Hacking Google Support: Leaking millions of customer records" for a bounty of $14,337 by @michaeldaltonau:https://t.co/mL1m89Zqef
— Awesome Google VRP Writeups (@gvrp_writeups) May 2, 2026
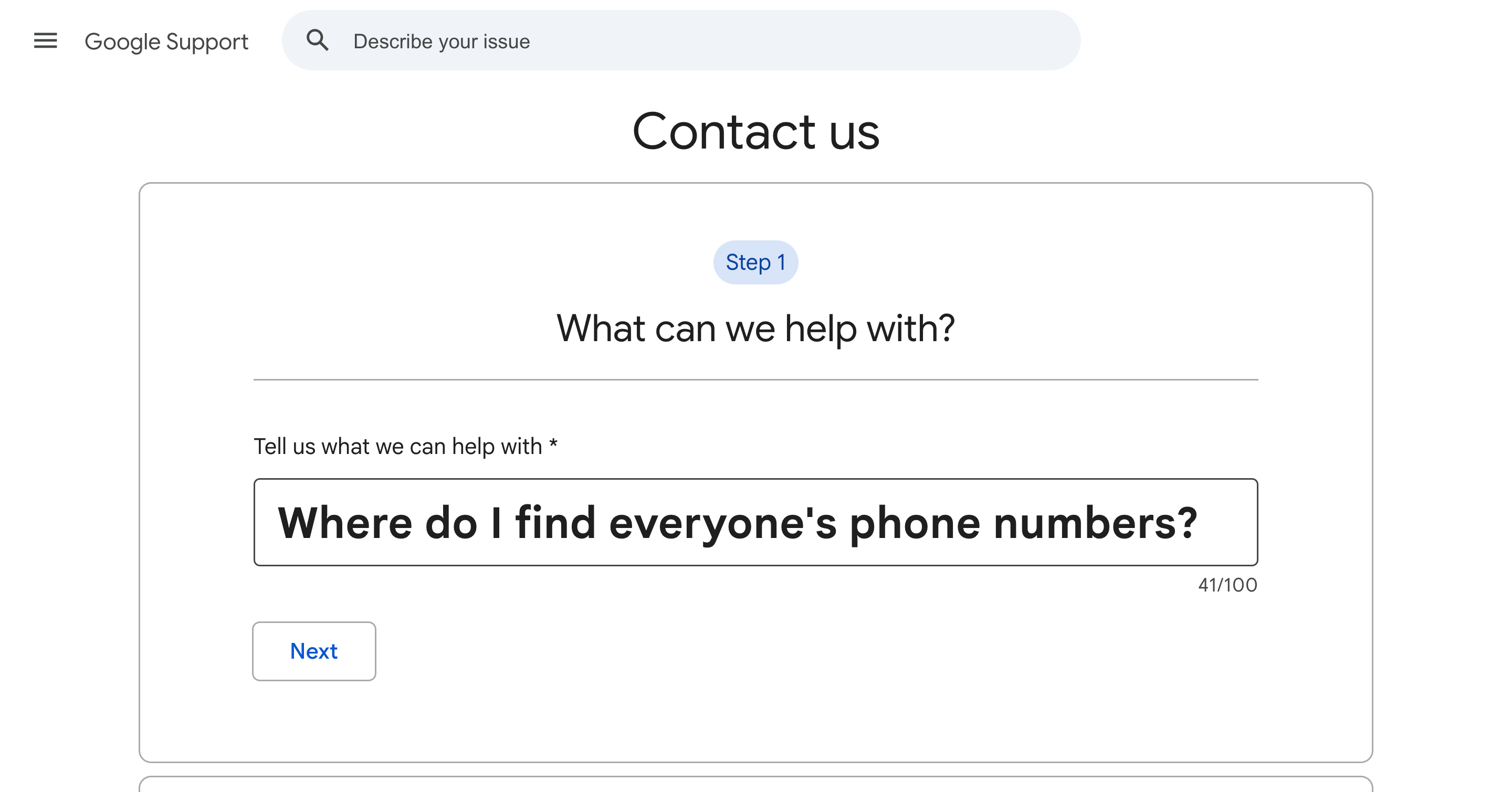
Hacking Google Support: Leaking millions of customer records ($14k bounty) | Michael Dalton
How I found my first vulnerability in Google - a way to leak private customer data for all cases in Google's internal support systems
Wild story unfolding around the KelpDAO hack funds frozen on Arbitrum.
— Vadim (AI, ⋈) (@zacodil) May 2, 2026
Quick context: in April, Lazarus Group (DPRK-linked) hacked KelpDAO for $292M via a LayerZero bridge bug. Some of the stolen ETH flowed through Arbitrum, and Arbitrum's Security Council froze $71M before the…
had way too much fun golfing https://t.co/ZsNohu7Kkc , so I made a website to compete with other peoplehttps://t.co/FvCopPQB9j
— Renato Marziano (@marspiterr) May 1, 2026
holding the WR at 492 bytes, please beat it (or pwn the website host for extra points)

Copy Fail — CVE-2026-31431
CVE-2026-31431. 100% Reliable Linux LPE — no race, no per-distro offsets, page-cache write that bypasses on-disk file-integrity tools and crosses containers. Found by Xint Code.
copy.golf — golf your exploits
shortest copy.fail payload wins. python scripts · ELF binaries · sandboxed VM.
Another great example of AI-driven vuln research finding high-impact bugs in a heavily audited open-source project.
— Alex Matrosov (@matrosov) May 2, 2026
Where human analysts give up or move on to a more interesting attack surface, AI keeps going until the end. Context, prompts, and skills still matter, but it’s not… https://t.co/AiDyQHePpO
so you’re telling me fighters in the desert need to move in strange ways to avoid the ire of an inescapable predator? https://t.co/ytNcCCLCIz
— Michael (Allegedly) (@MichaelAlleged) May 2, 2026
https://lore.kernel.org/all/CAMyZbw_ppC7F98+5huwmGjz03UGv8L8MoU9zL2_YYDU=fA3Qxw@mail.gmail.com/ https://lore.kernel.org/all/20260502211340.446927-1-n7l8m4@u.northwestern.edu/Two more issues/vulnerabilities allowing page cache overwrites in the Linux kernel. The first one below is confirmed by maintainers, the second didn't receive a reply yet.
— Anderson Nascimento (@andersonc0d3) May 2, 2026
[SECURITY] mm/userfaultfd: cross-inode page cache injection via mfill_copy_folio_retry()… pic.twitter.com/BrxUcjaNox
Mind blown 🤯
— Iceman (@herrmann1001) May 2, 2026
Some smartphones sold in mainland China (like certain OPPO models) can read MIFARE Classic cards, crack the keys in seconds, store them, and then fully emulate the card directly on the phone.
No extra hardware. Just the phone.
Access control, transit cards, hotel… pic.twitter.com/ypqckh8crk
Introducing What The Claude: Browser Edition.
— stratan (@5tratan) May 2, 2026
A series where we pick apart browser bugs found/reported by Claude.
First up: CVE-2026-2796, a SpiderMonkey Wasm import bug that leads to addrof/fakeobj/read-write.https://t.co/njBC5WEjq8
publications/research/firefox/CVE-2026-2796-wasm-call-bind-import-confusion at main · str8outtaheap/publications · GitHub
Security research writeups. Contribute to str8outtaheap/publications development by creating an account on GitHub.
str8outtaheap/publications (2 stars, JavaScript) Security research writeups
source: stratan (@5tratan)
As we’ve been covering for years, Putin’s efforts to control Russia’s information environment speak to insecurity about his own regime’s vulnerability to the sort of information warfare he wages against the West. https://t.co/ScViKAtv7E https://t.co/x3alIiI4Bk pic.twitter.com/JvagSug3zV
— Patrick Tucker (@DefTechPat) May 2, 2026
Russia Will Test Its Ability to Disconnect from the Internet - Defense One
The nascent RuNet is meant to allow the country to survive an attack — and Putin to monitor and control the population.
Filing this under "reverberations of the Iran war I had not anticipated" pic.twitter.com/tCICHf2YA2
— Ali Vaez (@AliVaez) May 2, 2026
Niels Provos posting smart security stuff, Dave Aitel knows stuff he can’t share, Halvar exploring the current space, and people arguing loudly about disclosure ethics..
— haroon meer (@haroonmeer) May 2, 2026
This could totally be 2002..
Just finished a really cool visit to Singapore! Where I met with a lot of the smartest folks here in the Vulnerability Research space. We are planning to build a new security hub in Singapore. And the first team we are building is going to be focused on..
— Eduardo Vela (@sirdarckcat) May 1, 2026
1/?🧵 https://t.co/Aw3HDP7jPW
Add a comment: