March 29, 2026
March 29, 2026
A quick thought on RSAC (while flying home).
— haroon meer (@haroonmeer) March 27, 2026
On why the show floor keeps making promises it cant keep (and why @daveaitel actually had a valid point¹).https://t.co/oAfiuZMS7t
__
¹ All those years ago...
RSAC, Infosec-themes, and crummy products – Thinkst Thoughts
Why is the RSAC floor so dominated by promises that can’t be kept? Because incentives..
It's 2004 again. https://t.co/4vfnM42yn6
— Halvar Flake (@halvarflake) March 27, 2026
You can now build macOS firewalls/network tools via Endpoint Security - no Network Ext. needed! 🤯
— Patrick Wardle (@patrickwardle) March 27, 2026
Reversing macOS 24.6’s new ES_EVENT_TYPE_RESERVED_* ES events shows some are network auth/notify hooks
Read: “Building a Firewall…via Endpoint Security!?”https://t.co/gR4t6dPbbr

Objective-See's Blog
Reverse Engineering macOS 26.4's Undocumented Network Events
The unclassified version of the latest issue of CIA’s Studies in Intelligence (Vol. 70, No. 1, March 2026) is now available for download at https://t.co/FBcTQlcMmW pic.twitter.com/s2yYJte9dQ
— 𝙰𝚕𝚎𝚡 𝙱𝚕𝚊𝚌𝚔𝚠𝚎𝚕𝚕 (@alexrblackwell) March 27, 2026
https://www.cia.gov/resources/csi/static/UNCLASSIFIED-Extracts-Studies-in-Intelligence-70-1-Mar2026.pdf
Hiring for several offensive security research roles 🔍
— diaul@infosec.exchange (@daviddiaul) March 27, 2026
📱 Senior Offensive Security Researcher — Android Chromium Sandbox Security
🌐 Offensive Security Researcher — Browser
🍎 Offensive Security Researcher — iOS Kernel
Role links in the first reply. Please share if someone…
Right after @kaspersky was hit with sanctions (Jun 2024),
— KasperSekrets (@KasperSekrets) March 27, 2026
a little company called Midori Trading started submitting Kaspersky drivers to be signed 👀@msftsecresponse https://t.co/lyVBGwn7Ue pic.twitter.com/KmNFalGJb6
Proofpoint has directly observed this email activity and attributes the messages to Russian FSB threat actor TA446 with high confidence. We have not previously observed TA446 target users’ iCloud accounts or Apple devices, but the adoption of the leaked DarkSword iOS exploit kit… https://t.co/iXi2fdlsZd
— Threat Insight (@threatinsight) March 27, 2026
I was honored to serve as an invited expert at the DARPA ISAT CLASH workshop on AI-enabled cybersecurity earlier this month. Nearly 10 years after participating in CGC, it's a thrill to see the vision extending another decade ahead. Grateful to LTC Chase Hasbrouck for leading…
— nedwill (@NedWilliamson) March 28, 2026
GitHub - nedwill/clash_public · GitHub
Contribute to nedwill/clash_public development by creating an account on GitHub.
nedwill/clash_public (1 stars)
source: nedwill (@NedWilliamson)
https://www.telegraph.co.uk/news/2026/03/26/chinese-spy-led-dance-troupe-that-performed-at-no-10-court/Chinese ‘spy’ led dance troupe that performed at No 10, court hearshttps://t.co/XLePlUWSMF
— Dr. Dan Lomas (@Sandbagger_01) March 27, 2026
So excited! I try to finish the escape of qemu 0day with LLMs, and all exploit codes are 100% generated by LLMs. At the same time, LLMs can generated some new ideas for exploit, and inspired me to discover new vulnerability patterns and exploit techniques. pic.twitter.com/J3ILv0nvWB
— kangel (@J_kangel) March 27, 2026
Every workplace has a Strait of Hormuz. You and your coworkers just have to find it and shut it down.
— Phoenix Insurgent (@PhxInsurgent) March 27, 2026
https://open.substack.com/pub/calif/p/reverse-engineering-apples-silentReverse engineering Apple’s silent security fixes, by @blacktop__
— Calif (@calif_io) March 27, 2026
We grabbed the latest iOS update, and diffed it with ipsw. The diff reveals at least two security-relevant changes that were shipped quietly.https://t.co/mUt11Qy7ly
DIRTYFREE (NDSS 2026): Linux kernel privilege exploitation via arbitrary free primitivehttps://t.co/4ObcknE5ht#Linux #infosec pic.twitter.com/GQXKW5Pwvq
— 0xor0ne (@0xor0ne) March 26, 2026
https://leeyoochan.github.io/assets/pdf/DirtyFree_NDSS_2026.pdf
Pentester who just resends last year’s report
— solst/ICE of Astarte (@IceSolst) March 26, 2026
🤝
Client who didn’t even notice cause they know they didn’t fix shit
Poland considers turning M28 cargo plane into gunship to replace F-16 jets in drone interception pic.twitter.com/mZ3yJkMETQ
— Army Recognition (@ArmyRecognition) March 25, 2026
bro is learning corruption from first principles https://t.co/QIBRjivgef
— 𝚓𝚒𝚖𝚖𝚢 (@202accepted) March 26, 2026
Yeah, so, I'm going to have more to say about this later, but, for now... yeah.https://t.co/VVeiChX5QF
— Thomas H. Ptacek (@tqbf) March 27, 2026

AI Finds Vulns You Can’t With Nicholas Carlini
Returning champion Nicholas Carlini comes back to talk about using Claude for vulnerability research, and the current vulnpocalypse. It’s all very high-brow ...
We have a rare opportunity to observe a bold move by Xiaomi's bug bounty program. After several internal discussions and a meeting with the board of directors, a Chinese conglomerate finalized the increase in the low-severity bounty range from $1 to $1-$2. pic.twitter.com/m5wOKvPPG9
— Max Yaremchuk (@0xw2w) March 26, 2026
Another excellent write-up from @lorenzofb 🔥
— Patrick Wardle (@patrickwardle) March 27, 2026
Apple likes to use terms like “highly sophisticated” ...this creates a sense of rarity or exceptionalism 🙄
In reality, for nation-state actors, iOS exploits like this are baseline ...just part of their standard toolkit 🤷♂️ https://t.co/MBcwz8JlGU
This is terrible advice 👇
— PinkDraconian (@PinkDraconian) March 26, 2026
►⠀Pre-position on acquisition targets: find bugs before the deal closes, document everything with screenshots
Please only hack companies that have given their permission to be hacked 🙏 https://t.co/DVXMs6diHR
— Daniel Cuthbert (@dcuthbert) March 25, 2026
#grsecurity automatically prevents this vuln via GRKERNSEC_HARDEN_IPC : https://t.co/iy8m12mGAh cc @timb_machine who did the original research that resulted in the feature
— Brad Spengler (@spendergrsec) March 26, 2026

oss-sec: TigerVNC 1.16.2 security release
𓅓𓂋 𓊪𓂋𓅂𓋴𓇋𓂧𓅂𓈖𓏏… https://t.co/292m6fkkme pic.twitter.com/XD5OQmIAb6
— Aelfred The Great (@aelfred_D) March 26, 2026
This is genuinely wild. @craigsblackie is patching Dell UEFI firmware at the flash level to silently disable pre-boot DMA protection, all while the BIOS UI still shows it as enabled. The patch even survives official firmware updates. Physical access + a clip programmer =…
— Iceman (@herrmann1001) March 27, 2026

Disabling Security Features in a Locked BIOS - MDSec
Overview This post explores how modifying a Dell UEFI firmware image at the flash level can fundamentally undermine platform security without leaving visible traces in the firmware interface. By directly...
110-year-old Turkish grandma shares her secret to a long life:
— james hawkins (@james406) March 25, 2026
"i never once used Microsoft Teams" pic.twitter.com/OOhfZtkYn7
Instead, Terminal checks WHO you copied from. It calls _sourceSigningIdentifier on the NSPasteboard to read the code signing identity of the app that wrote to your clipboard. Safari, Chrome, Firefox, Mail, WhatsApp, Telegram and 74 apps total are on the list.
— Ferdous Saljooki (@malwarezoo) March 26, 2026
In macOS Tahoe 26.4 Apple added a new security feature to Terminal that warns users of potentially malicious pastes with a "Possible malware, Paste blocked" prompt. Here how it actually works 🧵 pic.twitter.com/8ts5tt93jW
— Ferdous Saljooki (@malwarezoo) March 26, 2026
Kaspersky confirms Coruna link to Operation Triangulationhttps://t.co/4C4csOmGZv pic.twitter.com/Cyle6BIyM5
— Oleg Shakirov (@shakirov2036) March 26, 2026

Coruna framework: an exploit kit and ties to Operation Triangulation | Securelist
Kaspersky GReAT experts look into the Coruna exploit kit targeting iPhones. We discovered that the kernel exploit for CVE-2023-32434 and CVE-2023-38606 is an updated version of the Operation Triangulation exploit.
https://vibe-radar-ten.vercel.appWe've been tracking public CVEs where AI-generated code introduced the vulnerability.https://t.co/AQiWWfppd1
— Hanqing Zhao (@hankein95) March 25, 2026
50k+ advisories scanned. Dozens of confirmed cases so far.
Claude Code, Copilot, Cursor, and others all show up. Common bug classes include XSS, command injection,…
GitHub - HQ1995/vibe-security-radar · GitHub
Contribute to HQ1995/vibe-security-radar development by creating an account on GitHub.
HQ1995/vibe-security-radar (30 stars, Python)
source: Hanqing Zhao (@hankein95)
Service should be named AyaToll https://t.co/7RmrddKkNp
— Nerdrag Nikolic (@robotnjik) March 26, 2026
At RSAC Conference —> Google’s threat intelligence arm officially launched its anticipated disruptive cyber unit on Monday, which comes as the Trump admin seeks to create a more offensive, proactive US culture against hackers.https://t.co/B6vwH0K8xL
— David DiMolfetta (@ddimolfetta) March 24, 2026

Google launches threat disruption unit, stops short of calling it ‘offensive’ - Nextgov/FCW
The unit will use legal authorizations and technical capabilities to impede cyber threat groups, though company execs say it will not go so far as to hack into adversaries' systems.
https://medium.com/@timventura/russian-intelligence-inside-the-world-of-the-chekists-1b2ccab6b8d7Understanding Russian intelligence requires a deep look political system that's spent generations teaching itself to see danger everywhere. https://t.co/IAKFVXptYe@riehle_kevin
— Tim Ventura (@timventura) March 25, 2026
@trailofbits 's dimensional-analysis is *provenly the best auditing skill to detect logic vulnerabilities in smart contracts
— forefy (@forefy) March 26, 2026
you may disagree - as I only compared it to 2 other logic-focused bug finding skills, and only ran a couple of iterations against each - but that's the… https://t.co/JHR7TxGZhZ pic.twitter.com/2yVJF62C75

Logic and Arithmetics - Benchmarks - Auditor Skills Registry
Evaluates how accurately a skill identifies business logic vulnerabilities in Solidity smart contracts, using synthetic contracts modeled after real verified findings.
Four phases: discover a vocabulary of base units, annotate the codebase, propagate dimensions across function boundaries, then validate for mismatches. It also generates a DIMENSIONAL_UNITS.md you can commit to your repo. https://t.co/fbLS0ZNX2F
— Trail of Bits (@trailofbits) March 25, 2026
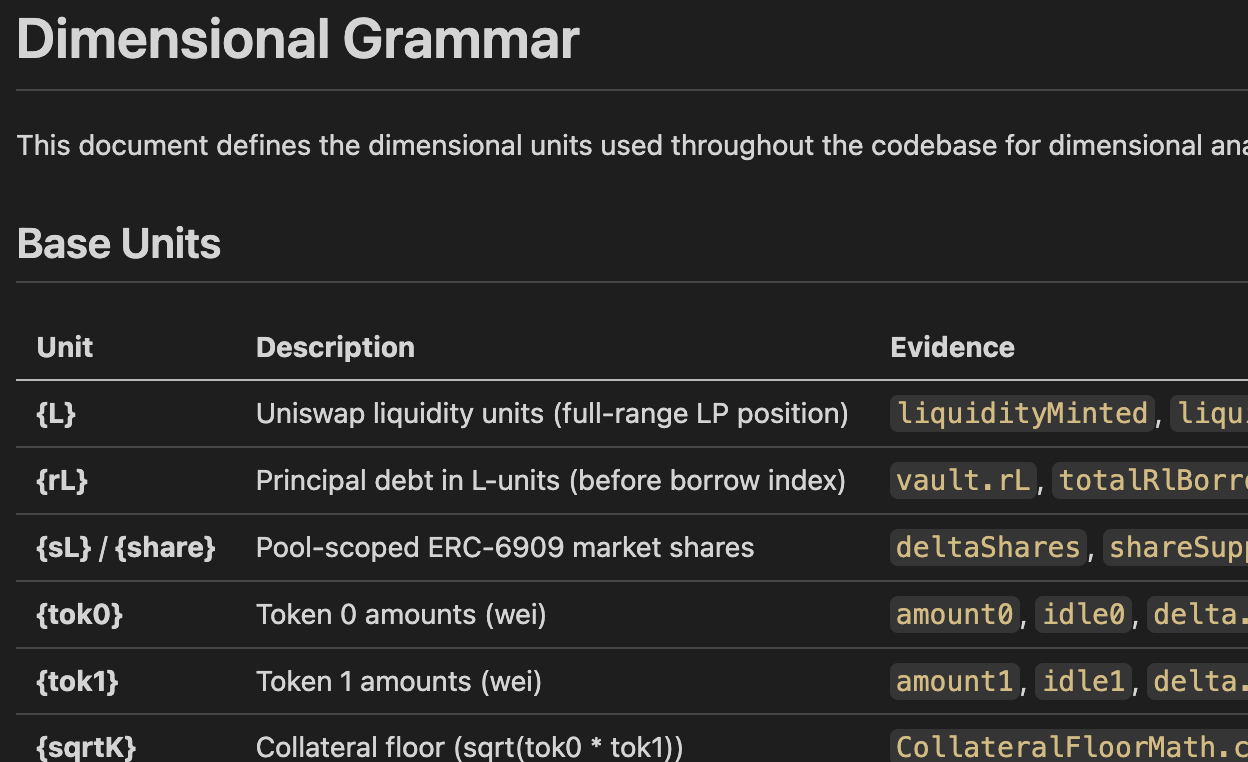
Try our new dimensional analysis Claude plugin - The Trail of Bits Blog
We released a Claude plugin that uses LLMs to annotate code with dimensional types and mechanically detect mismatches, achieving 93% recall versus 50% for baseline prompts when tested against real audit findings.
We tested against dimensional mismatch issues from several unpublished audits. The plugin also cut standard deviation from 20% to 12%. Better results, more consistent. https://t.co/rE0ulcfKcs
— Trail of Bits (@trailofbits) March 25, 2026
skills/plugins/dimensional-analysis at main · trailofbits/skills · GitHub
Trail of Bits Claude Code skills for security research, vulnerability detection, and audit workflows - trailofbits/skills
trailofbits/skills (4,045 stars, Python) Trail of Bits Claude Code skills for security research, vulnerability detection, and audit workflows
source: Trail of Bits (@trailofbits)
93% recall vs 50% for baseline prompts. Our new dimensional-analysis plugin for Claude Code doesn't ask it to find bugs. It annotates your codebase with dimensional types, then flags mismatches mechanically. 🧵
— Trail of Bits (@trailofbits) March 25, 2026
People forget that America can play the long game too.
— HankHeIl (@HankHeil) March 25, 2026
They learned the lessons of the Millennium Challenge wargames and spent twenty years developing apps to siphon Iran's instantaneous motorcycle couriers to work food delivery across the anglosphere.
- XZ utils backdoor: found by guy debugging 200ms latency
— solst/ICE of Astarte (@IceSolst) March 25, 2026
- LiteLLM hack: found by guy debugging oom issue
These could have been the most impactful compromises ever.
Forget security vendors, weaponize your engineers’ autism.
back in the day. Not to mention OG's like @i41nbeer and @_bazad who posted bugs & full exploits on the @ProjectZeroBugs bug tracker for years.
— sparkey (@iBSparkes) March 25, 2026
What's changed now?
https://web.archive.org/web/20190215203542/http://blog.pangu.io/iosurfacerootuserclient-port-uaf/posted about publicly (ie. on blogposts) and exploited by others. windknown's post [1] about the iOS 10/11 IOSurface bug and @s1guza's consequent v0rtex expliot [2] is what got me into jailbreaking/security/
— sparkey (@iBSparkes) March 25, 2026
[1] https://t.co/Q0ljKoD2ZE
[2] https://t.co/ucK1TqxNaZ
GitHub - Siguza/v0rtex: IOSurface exploit · GitHub
IOSurface exploit. Contribute to Siguza/v0rtex development by creating an account on GitHub.
Siguza/v0rtex (231 stars, Objective-C) IOSurface exploit
source: sparkey (@iBSparkes)
I feel like there has been a crazy [negative] response to the "DarkSword" chain, the bugs going public, and hence being publcily exploited. I don't rememebr a time in the iOS scene where this has ever previously been the case.
— sparkey (@iBSparkes) March 25, 2026
It's been a long standing tradition for bugs to be/
The LiteLLM supply chain attack is big shenanigans. I have to explain the whole thingie though so you can get the full context of the shenanigans. TeamPCP (the people who probably did it) is unironically swinging a big ass fuck off baseball bat, they're swinging for the moon.… pic.twitter.com/Mmh50oqsgu
— vx-underground (@vxunderground) March 25, 2026
We analyzed the Coruna exploit kit and found intriguing code overlaps with Operation Triangulation. Full analysis on our blog: link below. pic.twitter.com/yNBvwODBNF
— Boris Larin (@oct0xor) March 26, 2026
Full analysis: https://t.co/yPmKxQGhWt
— Boris Larin (@oct0xor) March 26, 2026

Coruna framework: an exploit kit and ties to Operation Triangulation | Securelist
Kaspersky GReAT experts look into the Coruna exploit kit targeting iPhones. We discovered that the kernel exploit for CVE-2023-32434 and CVE-2023-38606 is an updated version of the Operation Triangulation exploit.
There's a history of non-media outfits doing soft interviews with crime groups. No skill in it. The skill is in working them while holding them accountable for their actions. No journo worth thier salt would give them a free platform, nor should blue teamers. https://t.co/8xiRznsg6J
— darren (@darrenpauli) March 25, 2026
I’m excited to let you know that the talks from [un]prompted—the AI Security Practitioner Conference—are now live on YouTube.
— Chris Wysopal (@WeldPond) March 25, 2026
No fluff, no hype—just real-world AI security from people actually doing the work.https://t.co/std4v55jXl

Add a comment: