March 25, 2026
March 25, 2026
Russia hid spy hardware in the walls of TechEx, an Ukraine defense company that builds drones.
— MG (@_MG_) March 25, 2026
They don’t really explain what it is beyond “wire tap”, so let’s do a quick analysis on the hardware to configure out what it does!
🧵1 pic.twitter.com/F448pT2pjr
In these pictures, we see them removing what seems to be a wall mounted thermostat. Nothing to see yet…
— MG (@_MG_) March 25, 2026
🧵2 pic.twitter.com/YbYCsP99bf
Here we see the backside. The thermostat wire is at the very top. Just below is a white plate used to hide the spy hardware in question. Both have wires running down to a yellow low voltage junction box for power & network, which feeds in through the ceiling. You’ve all got… pic.twitter.com/60OtAiI3QI
— MG (@_MG_) March 25, 2026
… it’s a $7 IP Camera! 😂
— MG (@_MG_) March 25, 2026
We can see it’s plugged into power & network. But they also added a microphone to the audio input.
I want to know that the network line goes to. Another hidden device? Or more likely, back to TechEx’s own network? 😬 I have so many questions!
I… pic.twitter.com/SjCPBP83Rx
the orchestra could overpower the conductor if they really wanted to. it’s fear that holds them back
— chase (@_chase_____) March 24, 2026
If Iran offered him a revenue sharing agreement on a new Hormuz Strait shipping toll this would be over in a day.
— Jason, (@jasonc_nc) March 23, 2026
None of this is true. DailyDarkWeb is not conducting good faith journalism or research, there are no hard questions, no challenging of their responses - all this does is give a platform to threat actors to proliferate false-information. pic.twitter.com/ZPbDjk0FPj
— Silas Cutler (p1nk) (@silascutler) March 24, 2026
Compartmentation. The foundation of security. https://t.co/NXGxs1iYuD
— thaddeus e. grugq (@thegrugq) March 25, 2026
A lot of "software supply chain attacks" on developers become much less of a problem if the developer does not develop locally, but on a server they SSH into, and which does not contain any secrets. Just saying.
— Halvar Flake (@halvarflake) March 24, 2026
With worries about supply-chain attacks on the Python ecosystem, I wrote a few lines about my preferred development set-up, and how it adapts well to vibe-coding and mitigates many (if not all) risks.
— Halvar Flake (@halvarflake) March 25, 2026
https://t.co/hwzGDRhfpO — Halvar Flake (@halvarflake) March 25, 2026
ADD / XOR / ROL: Slightly safer vibecoding by adopting old hacker habits
I have seen a lot of public discussion around supply-chain attacks on the Python ecosystem, prompt injection risks when using coding agents,...
An automated N-day research pipeline at PwnFuzz.
— PwnFuzz (@pwnfuzz) March 24, 2026
Ghidra + Ollama + n8n →Diffs Patch Tuesday binaries → LLM analyzes the output → Structured vuln reports, monthly AI-generated reports gets you oriented fast!
Blog: https://t.co/O0EzQNdZev
Repo: https://t.co/wCFo8zoyeL pic.twitter.com/PsmUiTl1F6

N-Day Research with AI: Using Ollama and n8n | Nikhil's Cybersec Blog
GitHub - ghostbyt3/nday-automation-ai: This repository contains AI-generated analysis reports produced as part of an automated N-day research pipeline targeting Microsoft components. · GitHub
This repository contains AI-generated analysis reports produced as part of an automated N-day research pipeline targeting Microsoft components. - ghostbyt3/nday-automation-ai
ghostbyt3/nday-automation-ai (31 stars) This repository contains AI-generated analysis reports produced as part of an automated N-day research pipeline targeting Microsoft components.
source: PwnFuzz (@pwnfuzz)
Basically, if you start off with a system that makes it easy to create vulnerabilities it's unlikely that killing individual vulnerabilities–even if you can do it faster than before–will fix the underlying problem. (This doesn't mean you shouldn't try!)
— Brendan Dolan-Gavitt (@moyix) March 21, 2026
The blog post "Virtual Memory Tricks" by Niklas Gray explores clever, underutilized ways to leverage operating system virtual memory features (via APIs like VirtualAlloc or mmap) to solve common programming problems efficiently.
— Debasish (দেবাশিস্) Ghosh 🇮🇳 (@debasishg) March 21, 2026
Some of the key techniques discussed are ..
•…

Virtual Memory Tricks · Our Machinery
Some tricks you can do with virtual memory.
Sixty Russian agents identified: Prigozhin’s influence network taken over by the foreign intelligence service - Forbidden Stories https://t.co/Qkl5MGpK1u
— BUCSIS (@BUCSIS2) March 24, 2026
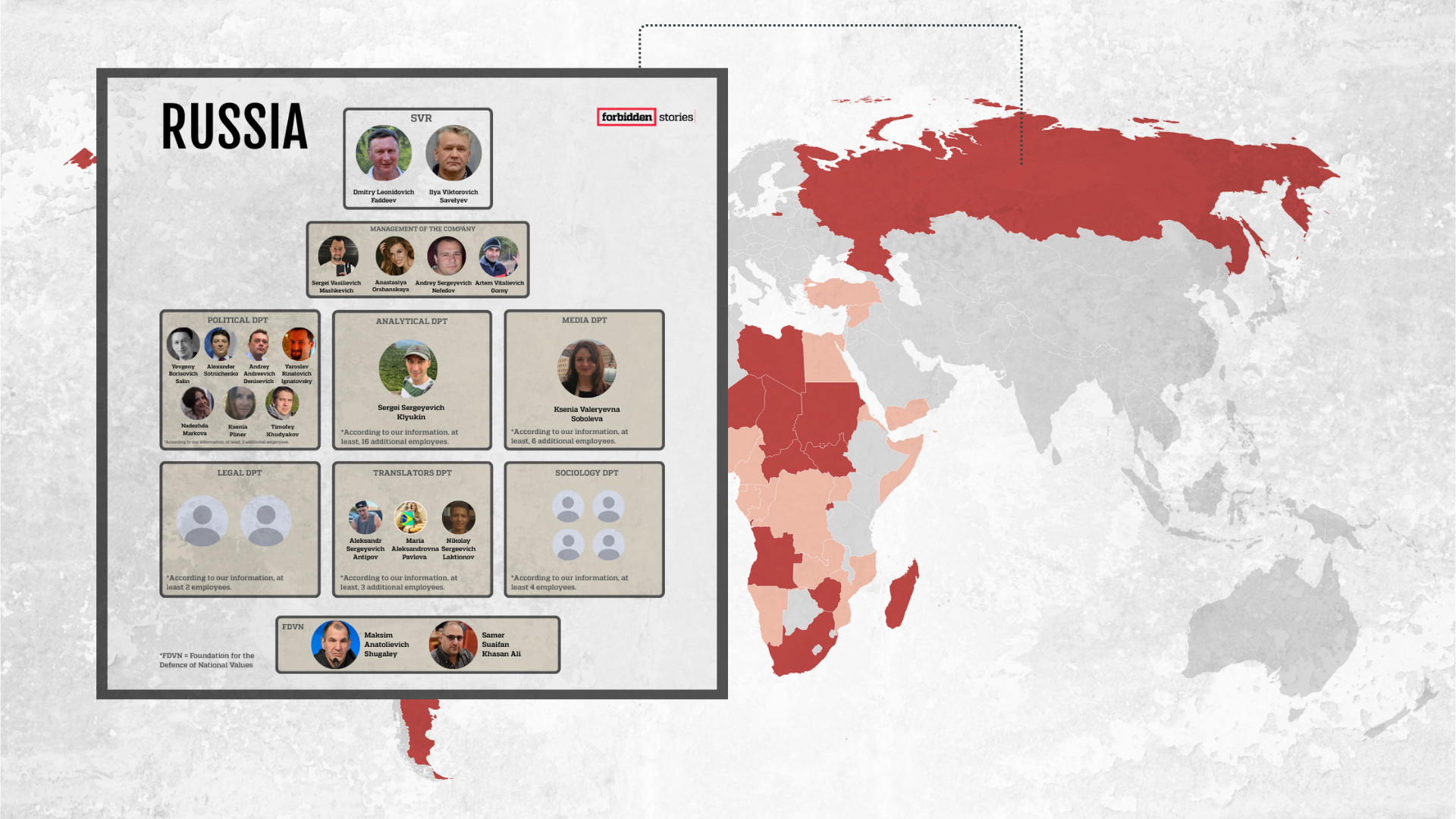
Sixty Russian agents identified: Prigozhin’s influence network taken over by the foreign intelligence service - Forbidden Stories
A data leak has allowed Forbidden Stories to identify more than 60 of its agents tasked with expanding Moscow’s disinformation efforts across three continents.
The glibc cycle continues lol..
— udp (@udp_ctf) March 23, 2026
Unsafe -> implement safety features -> safety features slow -> circumvent safety features in order to get speed -> unsafehttps://t.co/G0g5ZLtVNj
how2heap/glibc_2.42/tcache_metadata_hijacking.c at master · shellphish/how2heap · GitHub
A repository for learning various heap exploitation techniques. - shellphish/how2heap
shellphish/how2heap (8,540 stars, C) A repository for learning various heap exploitation techniques.
source: udp (@udp_ctf)
This 1-pager from Xusheng Li on GDB internals of how watchpoints are implemented is a delight to read! (especially that double-write behaviour false positive - I did not know about that) pic.twitter.com/4PcehQG9kg
— Gynvael Coldwind (@gynvael) March 24, 2026
Professors have approximately zero free time. And yet. 👀
— Zhiyun Qian (@pkqzy888) March 24, 2026
Turns out LLMs as super assistants make exploit dev manageable and fun again.
Pixel 10 root exploit (LPE) with an N-day. No public exploits exist for this thing.
Maybe I should teach a course on this. #LLM #ExploitDev pic.twitter.com/0Aff1ts3Tq
— Jacob Baines (@Junior_Baines) March 24, 2026
Time to invest in some GPUs and stop putting research in the cloud :) https://t.co/MLNvaD2ZZO
— Tarjei Mandt (@kernelpool) March 24, 2026
These two organisations have done more to move the world towards renewable sources of energy than every green party or ecological group in the world, combined. pic.twitter.com/yW0qfna6SH
— Damage Control (@Dmg_Cntrl) March 24, 2026
to all pwn2own gooners out there, headsup! in the last 4 hours litellm pypi package has been backdored and a bit of decoding shows, it steals almost every fucking key you got (that's the least it does)
— SinSinology (@SinSinology) March 24, 2026
*An attempt in this category might be launched from the local apt's laptop* https://t.co/c2YUa97Fqp pic.twitter.com/zqNMAKbLUT
I'll go through it during the week, but no doubt it is a great work from @v4bel, as always. Congratulations!
— Anderson Nascimento (@andersonc0d3) March 24, 2026
For historic purposes, I believe there were similar public vulnerabilities in the past and if you dig enough, you could learn about it. I can remember two issues… https://t.co/6RKnBJ9D6d
rxrpc: Restore removed timer deletion · torvalds/linux@ee3b082 · GitHub
A recent patch[1] from Eric Dumazet flipped the order in which the keepalive timer and the keepalive worker were cancelled in order to fix a syzbot reported issue[2]. Unfortunately, this enables t...
perf: Ensure swevent hrtimer is properly destroyed · torvalds/linux@ff5860f · GitHub
With the change to hrtimer_try_to_cancel() in perf_swevent_cancel_hrtimer() it appears possible for the hrtimer to still be active by the time the event gets freed. Make sure the event does a full...
I discovered a race-based vulnerability class in the Linux kernel: "Out-of-Cancel"
— V4bel (@v4bel) March 23, 2026
A structural flaw where cancel_work_sync() is used as a barrier for object lifetime management, causing UAF across multiple networking subsystems.
I wrote an exploit for CVE-2026-23239… pic.twitter.com/gYjNCpAriN
Out-of-Cancel: A Vulnerability Class Rooted in Workqueue Cancellation APIs | Project V4bel
Introduction
We at @verialabs built an autonomous CTF agent in a weekend and won 1st place at @BSidesSF 2026, solving all 52/52 challenges.
— stuxf (@stuxfdev) March 23, 2026
It races multiple AI models (Claude, GPT-5.4) in parallel, each in isolated Docker sandboxes with full CTF tooling. A coordinator LLM reads solver…
GitHub - verialabs/ctf-agent: Autonomous CTF solver that races multiple AI models in parallel. 1st place BSidesSF 2026. · GitHub
Autonomous CTF solver that races multiple AI models in parallel. 1st place BSidesSF 2026. - verialabs/ctf-agent
verialabs/ctf-agent (200 stars, Python) Autonomous CTF solver that races multiple AI models in parallel. 1st place BSidesSF 2026.
source: stuxf (@stuxfdev)
https://www.economist.com/united-states/2026/03/22/america-tells-private-firms-to-hack-backI wrote on the new US cyber security strategy. It's a short doc, light on detail, but clearly emphasises offensive cyber operations, including pre-emptive ones to disrupt threats at source & private-sector operations to "hack back", a legally perilous area https://t.co/JYDPq6ee9e
— Shashank Joshi (@shashj) March 23, 2026
Before AI, I can only have about 5 unfinished papers and 1 polished paper. AI boosted my productivity so much that I now have 136 unfinished papers and 1 polished paper.
— Khoa Vu (@KhoaVuUmn) March 23, 2026
open casket funeral but you gotta pay extra to see his feet https://t.co/YV9GlqhGPx
— Andrew Fleischman (@ASFleischman) March 23, 2026
Jim Hacker: Humphrey, I'm told there's a situation at Diego Garcia.
— Marianne 🔆🌲❤️🔥 (@GreatAbysmal) March 23, 2026
Sir Humphrey Appleby: Only geographically, Prime Minister.
Jim Hacker: Geographically?
Sir Humphrey Appleby: Yes. It's still in the Indian Ocean.
Jim Hacker: Humphrey, Iran fired missiles at it!
Sir…
Fwiw the problem was never that AI slop was going to overwhelm security teams: the problem was that having their hidden technical debt all called in at once was going to overwhelm them. Chrome having as many bugs as it still does is the perfect case example.
— Dave Aitel (@daveaitel) March 23, 2026
Add a comment: