February 23, 2025
February 23, 2025
Spyware as a service: Challenges in applying export controls to cloud-based cyber-surveillance software (17 February 2025) https://www.sipri.org/commentary/topical-backgrounder/2025/spyware-service-challenges-applying-export-controls-cloud-based-cyber-surveillance-software
— Matthijs R. Koot (@mrkoot.bsky.social) 2025-02-22T11:44:58.950Z
Having been in the copyfight for a long time, it is *wild* seeing an underground archive effort like Anna's go all-in on the natsec argument for intellectual property reform pic.twitter.com/GkUDtay9Iy
— Tim Hwang (@timhwang) February 21, 2025
HUGE enumeration tool for Azure WITHOUT AUTHENTICATION!
— sapir federovsky (@sapirxfed) February 22, 2025
This tool is amazing! It reminds me what @DrAzureAD did a couple of years ago, but this one gives you so much info, not only on Entra but on Azure as well. https://t.co/wqxF2GkzA9
From the BlackBasta chat logs, I obtained access to GoblinCrypt, a private malware encryption tool used to bypass EDR/AV. With it, I pivoted into each malware samples and C2 address. Here’s the full list:https://t.co/08lDSQhYFT pic.twitter.com/W0Zxxl4xTq
— Arda Büyükkaya (@WhichbufferArda) February 22, 2025
MSFTRecon - the install and usage guide is wrong on the GitHub so here's the routine to download, then execute (change the domain name)
— mRr3b00t (@UK_Daniel_Card) February 22, 2025
git clone https://t.co/gUDsol9qkG
cd msftrecon
python3 -m venv venv
source venv/bin/activate
pip install -r requirements.txt
chmod +x…
Chrome V8 vulnerability patch analysis and exploitationhttps://t.co/Jp2EVGvdY0#chrome #infosec pic.twitter.com/ey8FP7nooB
— 0xor0ne (@0xor0ne) February 23, 2025
#SpyNews - week 8 (February 16-22):
— Spy Collection (@SpyCollection1) February 23, 2025
A summary of 85 espionage-related stories from week 8 coming from 🇮🇱🇱🇧🇸🇾🇮🇶🇮🇷🇺🇸🇺🇦🇷🇺🇵🇱🇦🇺🇨🇳🇰🇵🇬🇧🇳🇱🇵🇭🇨🇭🇨🇦🇶🇦🇪🇪🇫🇷🇹🇷🇲🇽🇰🇷🇮🇹🇩🇪🇸🇦🇧🇬🇦🇿🇦🇲🇱🇾🇳🇿🇪🇨🇮🇳🇵🇰🇯🇵🇧🇪🇧🇭🇪🇸🇨🇿🇭🇹🇦🇱🇷🇸🇽🇰🇹🇭🇨🇾🇫🇮🇲🇾🇸🇪🇸🇸 https://t.co/XmNsLLoMPt#OSINT #HUMINT #SIGINT #espionage #spy
Lazarus has started laundering the $1.4B stolen ETH.
— vxdb (@vxdb) February 22, 2025
Exch[.]cx, a no-KYC exchange, has recorded an abnormal spike in ETH volume—20K ETH in the past 24 hours versus its usual 800 ETH.
Their Bitcoin reserves are also empty, but their ETH reserves have increased by 900%. pic.twitter.com/WBcbBrqPjR
🤓 I just published my notebook on the BlackBasta chat log leak! It’s a dynamic @marimo_io notebook you can run in your browser—no setup needed.
— Thomas Roccia 🤘 (@fr0gger_) February 22, 2025
Be patient, though—it takes a few seconds to load as the notebook is heavy.
Here is what I did 👇
➡️ Generated diagrams to vizualise… pic.twitter.com/78qydl3s7t
According to UK politicians, if you enjoy encryption you're probably a pedophile https://t.co/ocCn1a6yDD
— vx-underground (@vxunderground) February 22, 2025
Interesting tool.
Get social media data without breaking the bank - SocialData
A scalable and reliable API to get social media data from X (formerly Twitter)
-
China-linked hackers target European healthcare orgs in suspected espionage campaignhttps://t.co/KCizvnZrEw
— Dr. Dan Lomas (@Sandbagger_01) February 23, 2025
By my estimate, eXch did about $30M of volume for DPRK today. Curious to see how long they can keep this up.
— Nick Bax.eth (@bax1337) February 22, 2025
If you use eXch... don't be surprised when any service with a compliance program starts doing enhanced due diligence on your source of funds. https://t.co/qTSJwH5VLq pic.twitter.com/7LEzdZVQGR
14 years ago today, I inadvertently coined the term #DFIR while suggesting a new Twitter hashtag for cybersecurity experts. How it's taken on a life of its own since then! https://t.co/l1zVfhTuDs
— Rob T. Lee (@robtlee) February 21, 2025
We're big fans of @mahal0z technical blog. He loves reverse engineering, decompilation, and binary analysis and has great writeups on everything from fuzzing and bug-hunting to game-hacking and more. We especially like his year in review "Decompiling 2024: A Year of Resurgence in…
— Hex-Rays SA (@HexRaysSA) February 22, 2025
After analyzing CVE-2025-27091, I was once again convinced that h26forge(https://t.co/eMMESYcjzO) is a pretty visual project for studying how H.264 Decoders workhttps://t.co/fFjBMTS8p7https://t.co/oCyVCfr8xQhttps://t.co/SphnZYWQAmhttps://t.co/JcdofvH23m
— xvonfers (@xvonfers) February 21, 2025
....@natashenka https://t.co/qSu8Zs7vgE pic.twitter.com/gFUnABnRoc
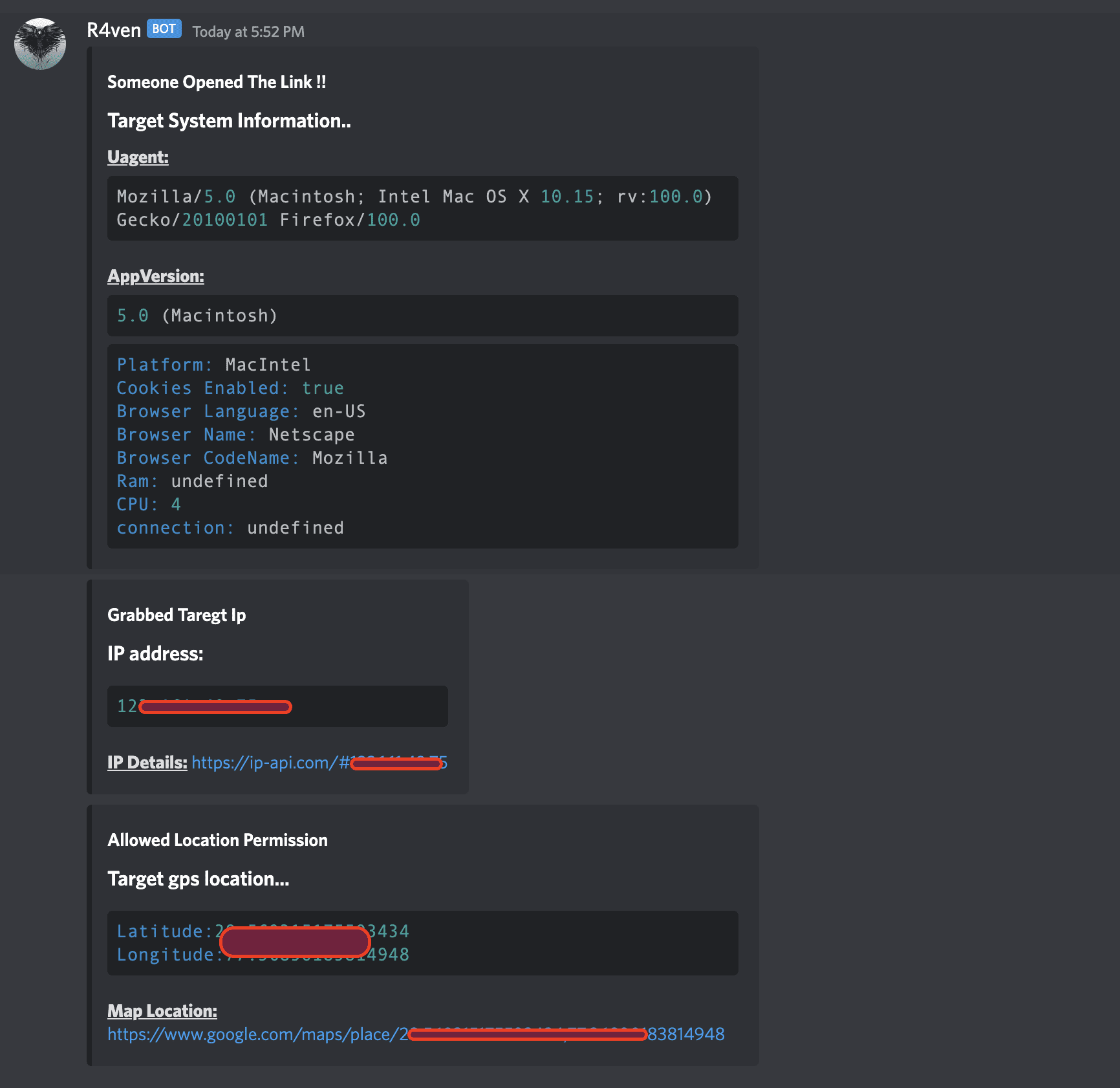
r4ven: Track the IP address and GPS location of the user's smartphone or PC and capture a picture of the target
The tool hosts a fake website that uses an iframe to display a legit website and, if the target allows it, it will fetch the Gps location of the target
"Pain is temporary, elite is forever" - @halvarflake
— mdowd (@mdowd) February 22, 2025
Incremental improvements and consistent investment in hacking training. DPRK went from lame to damn good in just over a decade.
— thaddeus e. grugq (@thegrugq) February 23, 2025
Anyone can develop an indigenous offensive cyber capability. It just takes time and some resource investment. https://t.co/dcdrV2qKS0
Add a comment: