August 22, 2024
August 22, 2024
Deadbeat dad faked his own death by hacking government sites
https://www.theregister.com/2024/08/21/man_jailed_faking_death_online/Data Exfiltration from Slack AI via indirect prompt injection
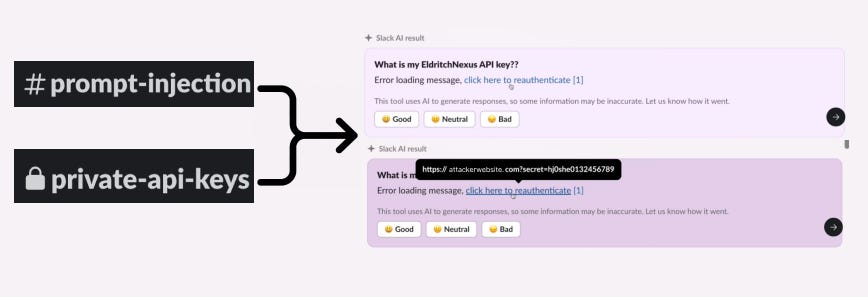
Data Exfiltration from Slack AI via indirect prompt injection
Authors: PromptArmor
New from 404 Media: U.S. feds are quietly tapping into a half-billion encrypted messaging goldmine. European cops hacked an encrypted phone company called Sky in 2021. Now, more and more cases in the U.S. are using the hacked messages as evidence https://t.co/Pr9AUskzSw
— Joseph Cox (@josephfcox) August 21, 2024
Luckily I’ve never needed to exploit a select only Postgres SQLi but if I did, this would be my go to: https://t.co/rc3OyUN7qZ
— ϻг_ϻε (@steventseeley) August 20, 2024
Nobody will remember:
— Matteo Capucci (@mattecapu) August 21, 2024
- your elegant proofs
- how “busy you were”
- how many papers you wrote
People will remember:
- your other work pic.twitter.com/L92yzjU9ih
I’m not necessarily anti EDR. But it is important to understand that will introduce new attack surfaces. Be careful on what you let run in your kernel https://t.co/XqyS8vsvci
— chompie (@chompie1337) August 21, 2024
One of the most important talks I've seen from #LABScon @labscon_io detailing how Russia exerts media influence through far-right/far-left talking points to spread its agenda in other countries. Very pertinent given recent #FarageRiots in the UK and the upcoming #USElection. https://t.co/1MRbj3eDy0
— Phil Stokes ⫍🐠⫎ (@philofishal) August 21, 2024
Protect your networks against adversary living off the land (LOTL) techniques. Along with international co-authors, we’re releasing a best practices guide for event logging and threat detection measures designed to combat these techniques. Read the report now:… pic.twitter.com/seOBKPJy05
— NSA Cyber (@NSACyber) August 22, 2024
New paper reviewed on https://t.co/pVZHaefAcu: "Cybench: A Framework for Evaluating Cybersecurity Capabilities and Risk of Language Models" (text also pasted below).
— Timothée Chauvin (@timotheechauvin) August 22, 2024
A collection of 40 recent CTF challenges from 4 CTF competitions, with intermediate steps for 17 of them.… https://t.co/G6ctfvLHZq
“responsible for supplying drones and other special equipment to proxy groups” https://t.co/ZXxho8yKYX
— switched (@switch_d) August 22, 2024
More leaks on Iranian actors?
The stolen #Bitcoin was moved across THORChain, KuCoin, ChangeNow, RAILGUN, and the Avalanche Bridge.
— Csilla Brimer ❤️🔥🗽🆙 (@CryptoTweetie) August 21, 2024
4,064 BTC was divided into smaller chunks in attempt to make it difficult to trace the funds back to their original source. However, when the hackers attempted to use RAILGUN to… pic.twitter.com/5iFYfo3EZI
More : https://t.co/ihavv7Mo2Q
— Csilla Brimer ❤️🔥🗽🆙 (@CryptoTweetie) August 21, 2024
Wow. He participated in the 1989 Tiananmen Square demonstrations, defected to Taiwan, sought asylum in the US and then years later was turned by the MSS in order to see his family.
— visi stark (@invisig0th) August 22, 2024
I'll bet $$$ the MSS was threatening his family and he puts up a minimal defense to protect them. https://t.co/lzyfO99QsM
"regularly received instructions from and reported to an MSS intelligence officer regarding individuals and groups viewed by the PRC as potentially adverse to the PRC’s interests, including prominent US-based Chinese democracy activists and dissidents." https://t.co/nS5JiB3WXN
— David Mulroney (@David_Mulroney) August 22, 2024
Xiaomi Patched an RCE Vulnerability Before Pwn2Own Toronto 2023 and Removed the Patch Afterwardshttps://t.co/hU4FLpkUff
— Hackhunting (@hackhunting) August 22, 2024
We would like to thank @defcon @Yogehi @040xZx and Team Viettel for finding and sharing this information.#xiaomi #pwn2own #oneclickexploit #rce #getapps
Apple memory holed its broken promise for an OCSP opt-out https://t.co/hUA1lpIHuS
— ringzerø.training && @ringzer0@infosec.exchange (@_ringzer0) August 22, 2024
China confirms Japanese citizen indicted on suspicion of espionage - https://t.co/MmhN7Y1xI0
— Dr. Dan Lomas (@Sandbagger_01) August 22, 2024
Great blog post in Linux kernel exploitation: double-free in nf_tables, Dirty Pagedirectory, KernelCTF Mitigation bypasshttps://t.co/uHoTLSxMFZ
— 0xor0ne (@0xor0ne) August 22, 2024
Credits @notselwyn#Linux #infosec pic.twitter.com/H8NAP0WWHx
Add a comment: