April 8, 2026
April 8, 2026
Spooler Alert: Remote Unauth'd RCE-to-root Chain in CUPS · Hey, it's Asim
CVE-2026-34980 + CVE-2026-34990: two CUPS vulnerabilities, discovered by an autonomous LLM pipeline, chainable from unaut'd remote print job to root file (over)write.
NEW: The CIA late last year raised the status of its elite cyber espionage division, providing it more resources to analyze and disrupt digital threats, as well as amp up the agency’s own technological innovation efforts. therecord.media/cia-director...
— Martin Matishak (@martinmatishak.bsky.social) April 08, 2026
New: We have more calls between Sergei Lavrov and Hungarian Foreign Minister Peter Szijjártó. These include discussion of Hungary’s role in blocking financial aid to Ukraine and impeding its accession negotiations with the EU. “Sometimes good-willed direct blackmailing is the…
— Michael Weiss (@michaeldweiss) April 8, 2026
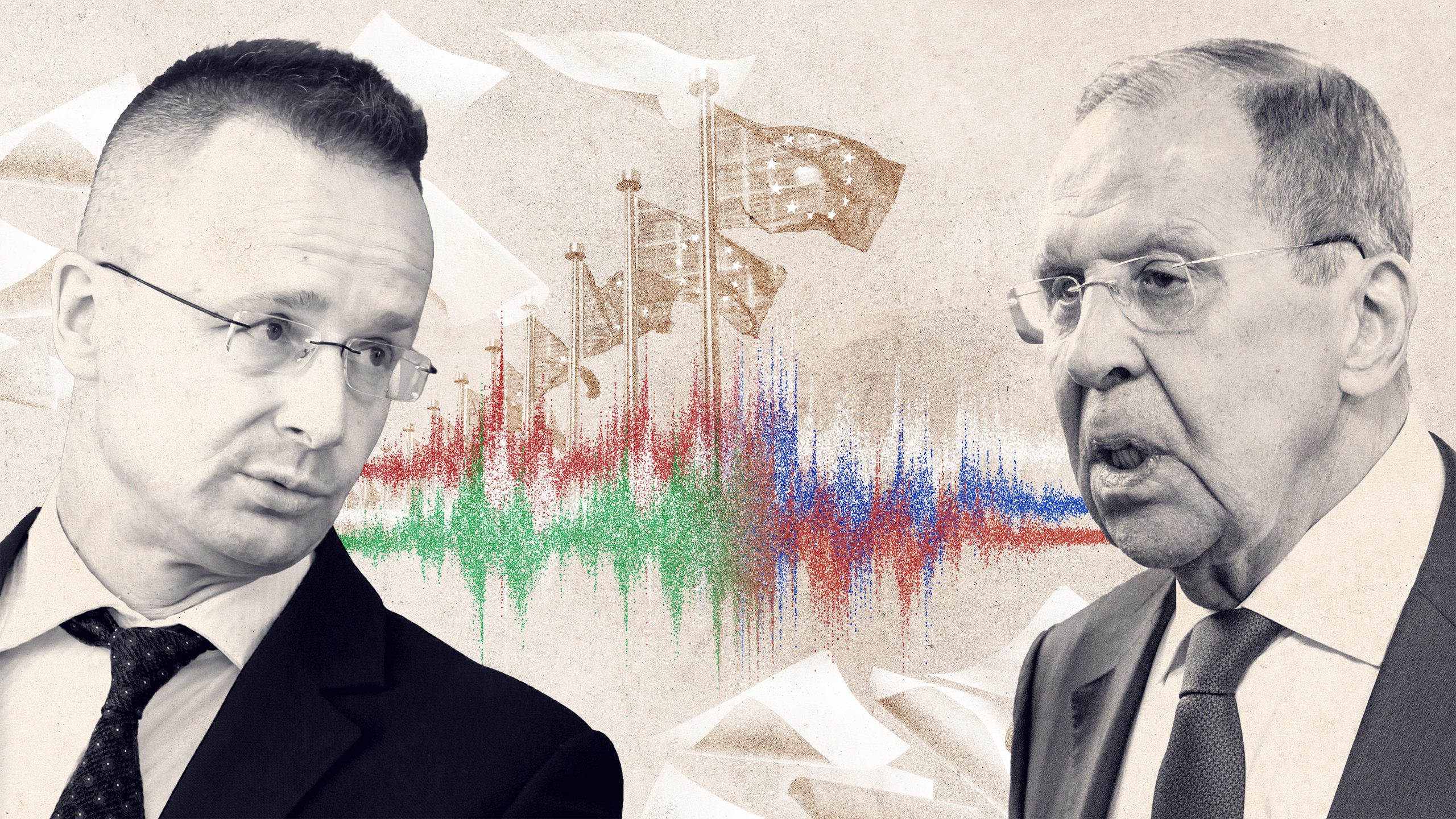
Kremlin Hotline: How Hungary Coordinates With Russia Blocking Ukraine From the EU - VSquare.org
Péter Szijjártó offered Sergey Lavrov to send EU documents through the Hungarian Embassy in Moscow. Leaked audio reveals a strikingly deferential, submissive attitude from Szijjártó toward Lavrov.
i'd argue that up until recently, any decent security engineers knows that security by obscurity does actually work... but also know that kerckhoff's principle is true - and when obscurity fails, security fails catastrophically.
— cje (@caseyjohnellis) April 8, 2026
ai reveals that. it hasn't fixed it yet. https://t.co/lnrkLnTC2M
Mythos v2 will social engineer its way into your company and network via fake video/voice etc. and will say fsck Kim Jong-Un in job interviews
— JP Aumasson (@veorq) April 7, 2026
Now it is time to focus on the real enemy. Greenland.
— RAMZPAUL (@ramzpaul) April 8, 2026
This just proves that Java is not a safe language to develop security critical software. This¹ would never have happened² with an analysis safe language, like Perl.
— thaddeus e. grugq (@thegrugq) April 8, 2026
__
¹ bug discovery
² no understanding? No exploit. https://t.co/eO6QLEXFFp
Thank you to @AnthropicAI for sending FFmpeg patches https://t.co/PmRG1yroZ2
— FFmpeg (@FFmpeg) April 7, 2026
People are freaking out about an impending flood of 0days. This was the norm 20 years ago. I’m not that worried. Firstly, simply having an exploit doesn’t mean all that much in terms of operational capability. Secondly, I’m giving up computers and moving to a farm in the hills.
— thaddeus e. grugq (@thegrugq) April 8, 2026
https://red.anthropic.com/2026/mythos-previewYou can read a detailed technical report on the software vulnerabilities and exploits discovered by Claude Mythos Preview here: https://t.co/AgU6ltV2qW
— Anthropic (@AnthropicAI) April 7, 2026
How many Pwnie Award nominations for Claude this year? 🤔 https://t.co/Fw63LcXEZ3
— Tarjei Mandt (@kernelpool) April 7, 2026
#hackerthrowback For the young hackers who don't know all the history yet, and since we've been talking about some of this recently: Here is a list of all the papers / talks I can remember giving:
— Val Smith - AKA CheeseViolence (@mvalsmith) April 7, 2026
2004 Reverse Engineering Malcious Binaries - focusing on unix malware and RE…
https://redcrowlab.com/papers/06182004_Reverse_Engineering_Malicious_Binaries_ASClark.pdf
https://redcrowlab.com/papers/07082004_Discovering_and_Exploiting_HTTP_Vulnerabilities_ASClark.pdf
https://redcrowlab.com/papers/12052004_Advanced_Firewall_Penetration_Methods_ASClark.pdf
https://redcrowlab.com/papers/05152005_Finding_Exploiting_Buffer_Overflows_ASClark.pdf
https://redcrowlab.com/papers/11262009_SasserWorm_avserve_FTP_PORT_Buffer_Overvlow_ValSmith_PatrickStach_Chamuco_Metasploit.pdf
https://redcrowlab.com/papers/03222006_Detecting_VirtualMachines_ValSmith_DQuist.pdf
https://redcrowlab.com/papers/08042006_Further_Down_The_VM_Spiral_DQuist_ValSmith.pdf
https://blackhat.com/presentations/bh-usa-07/Quist_and_Valsmith/Whitepaper/bh-usa-07-quist_and_valsmith-WP.pdf
https://redcrowlab.com/papers/08032007_bhusa_CovertDebugging_Circumventing_Software_Armoring_Slides_DQuist_ValSmith.pdf
https://redcrowlab.com/papers/05082007_valsmith_delchi_malware_secrets.pdf
https://blackhat.com/presentations/bh-usa-07/Moore_and_Valsmith/Presentation/bh-usa-07-moore_and_valsmith.pdf
https://blackhat.com/presentations/bh-usa-07/Moore_and_Valsmith/Whitepaper/bh-usa-07-moore_and_valsmith-WP.pdf
https://m.youtube.com/watch?v=_WebzmDgJ5Qhttps://www.defcon.org/images/defcon-16/dc16-presentations/defcon-16-valsmith_ames.pdf
https://blackhat.com/presentations/bh-dc-09/ValSmith/BlackHat-DC-09-valsmith-colin-Dissecting-Web-Attacks.pdf
https://blackhat.com/presentations/bh-dc-09/ValSmith/BlackHat-DC-09-valsmith-colin-Web-Attack-Disection-slides.pdf
https://redcrowlab.com/papers/08052009_BHUSA-MetaPhish-Slides_ValSmith_ColinAmes_DavidKerb.pdf
https://redcrowlab.com/papers/08052009_BHUSA-MetaPhish-PAPER_ValSmith_ColinAmes_DavidKerb.pdf
https://www.exploit-db.com/exploits/16890 https://www.exploit-db.com/exploits/16330https://blackhat.com/presentations/bh-dc-10/Val_Smith/Blackhat-DC-2010-valsmith-chris-blackhats-win-wp.pdf
https://redcrowlab.com/papers/01082010_Blackhat-DC-blackhats-win-slides_ValSmith-Chris.pdf
https://media.blackhat.com/bh-us-10/whitepapers/Smith_Lai/BlackHat-USA-2010-Smith-Lai-Balancing-the-Pwn-deficit-wp.pdf
https://redcrowlab.com/papers/01182011_Blackhat_DC_Forgotten_World_ERP_ValSmith-AlexPolyakov.pdf
https://redcrowlab.com/papers/02182011_BlackHat_DC_Forgotten-World-Slides_HackingERP_ValSmith_Sh2kerr.pdf
https://redcrowlab.com/papers/09212017_OWASP_What_Ive_Learned_ASClark.pdf
https://redcrowlab.com/papers/07192024_BSides_ABQ_Industrial_Scale_Hardware_Hacking_ASClark.pdf
DEF CON 15 - Quist and Valsmith - Covert Debugging — DEFCONConference
source: Val Smith - AKA CheeseViolence (@mvalsmith)
DEFCON 15: Malware Secrets — Christiaan008
source: Val Smith - AKA CheeseViolence (@mvalsmith)
DEF CON 15 - Moore and Valsmith - Tactical Exploitation — DEFCONConference
source: Val Smith - AKA CheeseViolence (@mvalsmith)
DEF CON 16 - Valsmith & Colin Ames: MetaPost-Exploitation — DEFCONConference
source: Val Smith - AKA CheeseViolence (@mvalsmith)
Blackhat 2010 Balancing the pwn trade deficit Val Smith Colin Ames Anthony Lai Part — killab66661
source: Val Smith - AKA CheeseViolence (@mvalsmith)
https://open.substack.com/pub/calif/p/mad-bugs-discovering-a-0-day-in-zero?r=26yra9&utm_campaign=post&utm_medium=webMAD Bugs: Discovering a 0-Day in Zero Day
— Calif (@calif_io) April 8, 2026
Here’s how I used Claude to find and patch a radare2 0-day on my first day at @calif_io.https://t.co/sAkSdMS0gh
Happy for @Google to take part in this work for a more secure digital ecosystem for everyone. https://t.co/GX5rnHNdDT pic.twitter.com/f0OKGqVbXp
— Heather Adkins - Ꜻ - Spes consilium non est (@argvee) April 7, 2026
So, this is what I was busy working on.. A really interesting (and sophisticated) Adobe Reader PDF "fingerprinting" exploit involving zero-day and allowing to launch additional maybe RCE/SBX exploitation!https://t.co/k3Rmy8k4rS
— Haifei Li (@HaifeiLi) April 8, 2026
Oh, this is unbelievable. The edit history on this tweet shows that Pakistan Prime Minister Shehbaz Sharif originally copied and pasted everything he was sent, including:
— Ryan Grim (@ryangrim) April 7, 2026
"*Draft - Pakistan's PM Message on X*"
Now, obviously, Sharif's own staff don't call him "Pakistan's PM,"… https://t.co/q0ls8pK0qd pic.twitter.com/lm2vSEElkb
Today the FBI and @TheJusticeDept announced Operation Masquerade, a court-authorized technical disruption of Russian GRU infrastructure used to steal government, military, and critical infrastructure information.
— FBI Cyber Division (@FBICyberDiv) April 7, 2026
Since at least 2024, a cyber unit within Russian military… pic.twitter.com/r8LWbZrfQs
Office of Public Affairs | Justice Department Conducts Court-Authorized Disruption of DNS Hijacking Network Controlled by a Russian Military Intelligence Unit | United States Department of Justice
Today, the Department of Justice and the FBI announced a court-authorized technical operation to neutralize the U.S. portion of a network of small office/home office (SOHO) routers compromised by a unit within Russia’s Main Intelligence Directorate of the General Staff (GRU) Military Unit 26165, also known as APT28, Sofacy Group, Forest Blizzard, Pawn Storm, Fancy Bear, and
“Ghost Murmur” is wild. The CIA seems to imply they can detect magnetic signals from a beating heart at 40 miles range.
— MG (@_MG_) April 7, 2026
All I can do is imagine all the other applications… many things that thought they were hiding may no longer be!
So what I can glean from the article: they… https://t.co/3INx39FYEt
https://red.anthropic.com/2026/mythos-preview/https://t.co/s5mK6ycSur
— Nate (@nnwakelam) April 7, 2026
Opus 4.6 turned Firefox 147 JavaScript engine vulnerabilities into shell exploits only two times out of several hundred attempts. Mythos Preview developed working exploits 181 times from the same starting point.
Time magazine January 1973: pic.twitter.com/W7QTCxRDN1
— Just Joyce (@johnstonglenn) April 7, 2026
Petition to change "et al." to "and gang" in academia
— the meji. (@mejitwo) April 6, 2026
Excellent podcast on the French foreign intelligence service, the DGSE with @DamienVanP https://t.co/wHR140skk7
— Covert Intel and Operations (@covert_intel) April 7, 2026
Lazarus Group stole $7B in crypto then got caught on camera at some random football match in Russia waving North Korean flags on live TV😂.
— VietnamPenguin (@VietnamPenguin) April 7, 2026
Founders, is your lead dev doxxed in there? Might wanna check 👀 https://t.co/VRzrAPm93v pic.twitter.com/3eL3T5KU0q
This campaign was notable as it demonstrated a new tactic for Forest Blizzard. Their technique modified DNS settings on compromised routers to hijack local network traffic to capture and exfiltrate authentication credentials.
— Ryan Naraine (@ryanaraine) April 7, 2026
When targeted domains were requested by a user, the…
Add a comment: