April 4, 2026
April 4, 2026
Iran Imposes New ‘Cash, Grass, Or Ass’ Fee For Strait Of Hormuz
— The Onion (@theonion.com) April 03, 2026
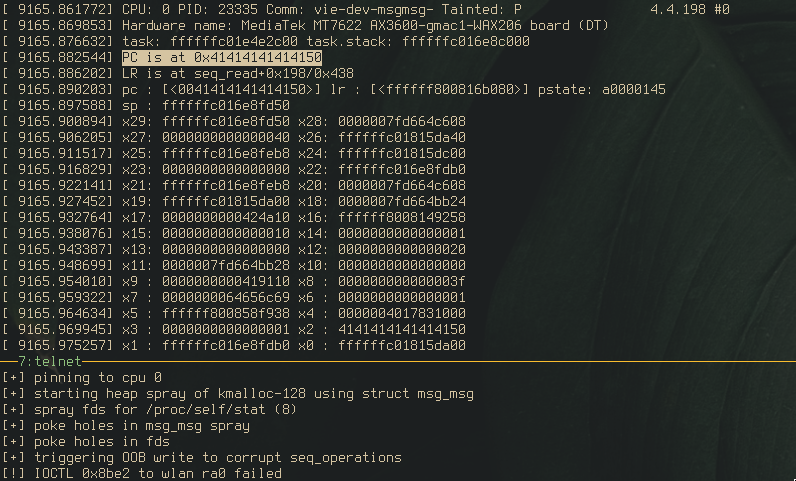
kernel alchemy pt. 1: developing exploit primitives with CVE-2025-20741 | hyprblog
Part 1 in a small series of posts covering the development of kernel exploit primitives, demonstrated with a few bugs in the Mediatek MT76xx wifi driver.
これは私の父が作った猪除けの猪です。 pic.twitter.com/ggpH1csAtN
— コマkoma (@watagashi4) April 3, 2026
If you are interested in how EDRs are bypassed in real world malware:https://t.co/qEskJ4OPb3
— Holger Unterbrink (@hunterbr72) April 2, 2026
Qilin EDR killer infection chain
This blog provides an in-depth analysis of the malicious “msimg32.dll” used in Qilin ransomware attacks, which is a multi-stage infection chain targeting EDR systems.
New post is up! This one uses CVE-2025-20741 (a heap overflow in the MediaTek MT76xx driver) to show how a bit of kernel alchemy can turn a heap OOB write into a number of stronger exploit primitives, up to page-level r/w via pipe_buffer corruption :)https://t.co/rA7nKZex5U
— hypr (@hyprdude) April 3, 2026
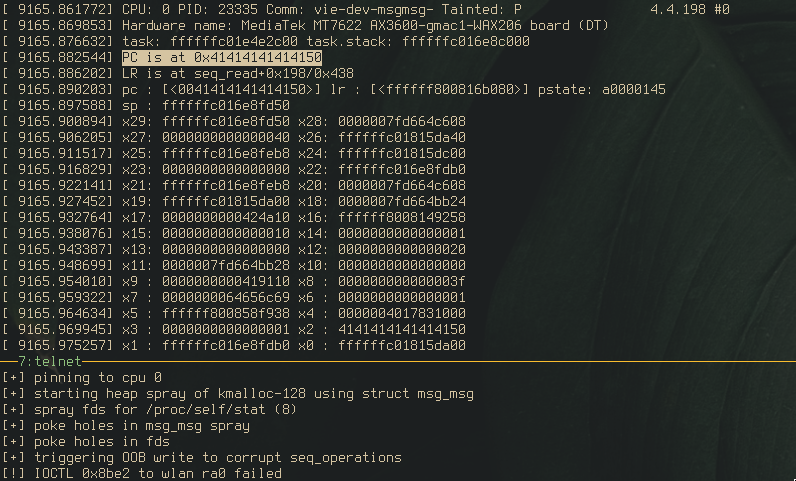
kernel alchemy pt. 1: developing exploit primitives with CVE-2025-20741 | hyprblog
Part 1 in a small series of posts covering the development of kernel exploit primitives, demonstrated with a few bugs in the Mediatek MT76xx wifi driver.
NEW: More than 500 members of the British armed forces stationed at the UK's most sensitive military sites have exposed their location data and personal details on Strava this year.
— Richard Holmes 🕵🏻♂️ (@Richard_AHolmes) April 3, 2026
Staff at the British Army HQ in Northwood, a surveillance and intelligence facility in North…

Hundreds of UK soldiers exposed at military bases… by their Strava workouts
StravaLeaks UK: The popular fitness app is revealing details from inside sensitive sites
This is Major Tom to tech support
— Law in Japan (@Colin_P_A_Jones) April 2, 2026
I’m clicking on the tab
But it’s acting in a most peculiar way
And the menu ribbon looks quite different today
https://deadeclipse666.blogspot.com/2026/04/public-disclosure.htmlPublicly disclosing the bluehammer exploit, at the time of writing this, this vulnerability is still unpatched.
— Chaotic Eclipse (@ChaoticEclipse0) April 3, 2026
Full PoC source can be found here - https://t.co/yk80ylIfBV
Here's all 4 exploits for yesterday's 6.6 LTS kernel in one tweet:
— Brad Spengler (@spendergrsec) April 3, 2026
fgetxattr(31337, NULL, NULL, 0);
flistxattr(31337, NULL, 0);
fremovexattr(31337, "very stable");
fsetxattr(31337, "so stable", 10, XATTR_CREATE);
Add a comment: