
April 20, 2026
April 20, 2026 Administrivia Sorry for the delays and then this huge post. Twitter changed their API slightly and ithe python module I use for scraping had...

April 19, 2026
April 19, 2026 Administrivia Sorry for the delays and then this huge post. Twitter changed their API slightly and ithe python module I use for scraping had...

April 19, 2026
April 19, 2026 Administrivia Sorry for the delays and then this huge post. Twitter changed their API slightly and ithe python module I use for scraping had...

April 16, 2026
April 16, 2026 FBI trolls Russian embassy with geotargeted ads for disgruntled spies - Ars Technica “Speak plainly… we are ready to listen.”... Xu Zewei...
April 15, 2026
April 15, 2026 Adobe Security Bulletin Prenotification Security Advisory for Adobe Acrobat and Reader | APSB26-44

April 14, 2026
April 14, 2026 https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=fdcbb1bc06508eb7ad961b3876b16382ae678ef8 HAPPENING NOW: Barbed...
April 13, 2026
April 13, 2026 http://geer.tinho.net/fgm/fgm.geer.1504.pdf https://blog.calif.io/p/claude-humans-vs-nginx-cve-2026-27654

April 12, 2026
April 12, 2026 “Our people poisoned Navalny”: Former FSB officer on surveilling opposition figures and running black ops in Russia and Ukraine — The Insider...

April 11, 2026
April 11, 2026 Bangkok Post - German hacker facing 74 cybercrime warrants arrested in Bangkok Police in Bangkok have arrested a German man facing 74 arrest...

April 10, 2026
April 10, 2026 Little Snitch for Linux Discover powerful applications such as Little Snitch Mini, Little Snitch, LaunchBar and Micro Snitch. Russian...
April 8, 2026
April 8, 2026 Spooler Alert: Remote Unauth'd RCE-to-root Chain in CUPS · Hey, it's Asim CVE-2026-34980 + CVE-2026-34990: two CUPS vulnerabilities, discovered...
April 7, 2026
April 7, 2026 fml-inc/panopticon (2 stars, TypeScript) Awkward scenes aboard Artemis II as Trump stops ranting and none of the astronauts have anything left...
April 6, 2026
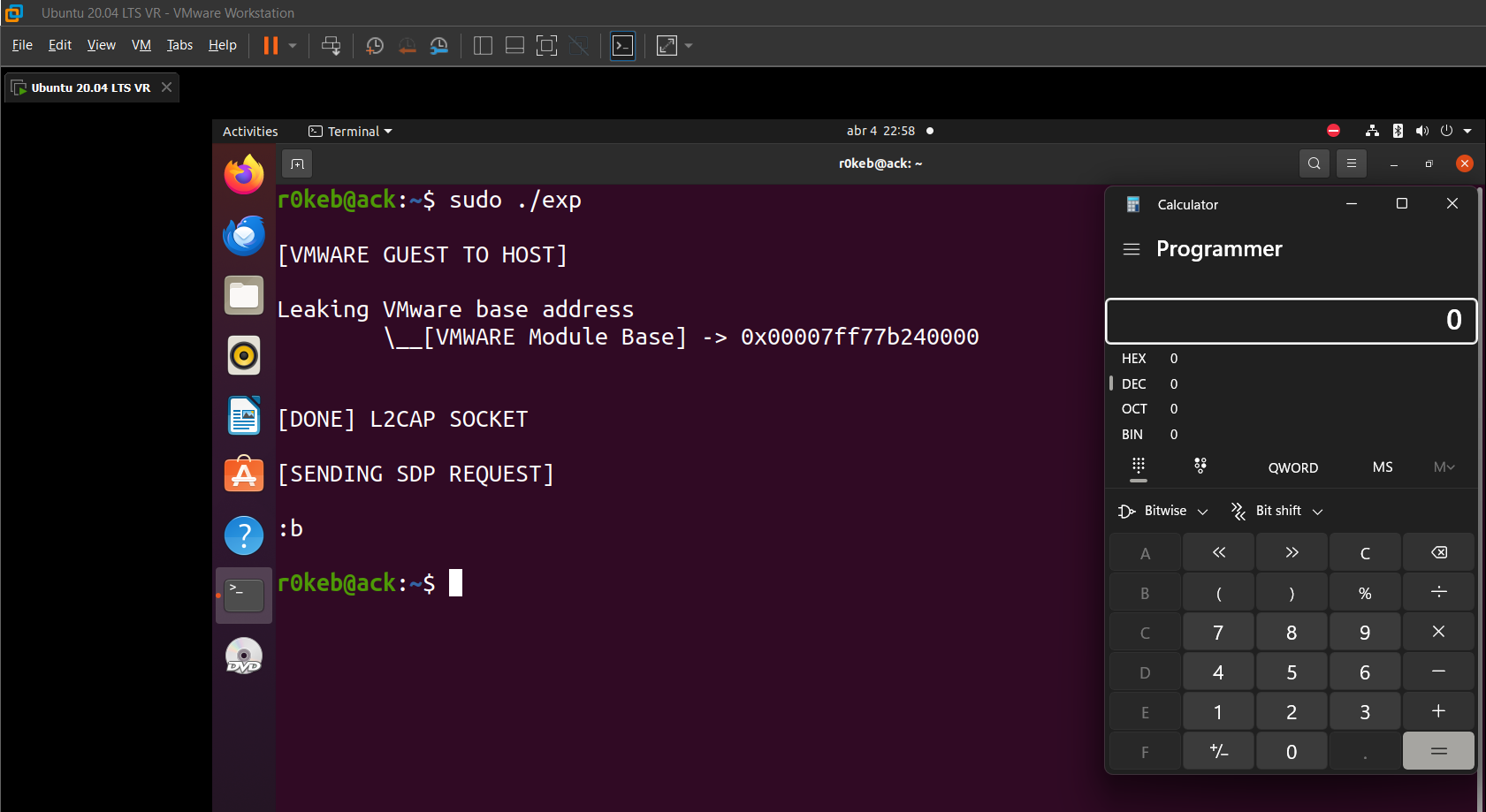
April 6, 2026 https://t.co/so573d0tzG ← my new old talk was released as a standalone; it's a fun story of how you go from being able to write '2' (0x32, 1...

April 5, 2026
April 5, 2026 https://t.co/qYBMCup9i6 — Drift (@DriftProtocol) April 5, 2026 A fact I hope no one ever needs to use but the way thugs track down Starlink...
April 4, 2026
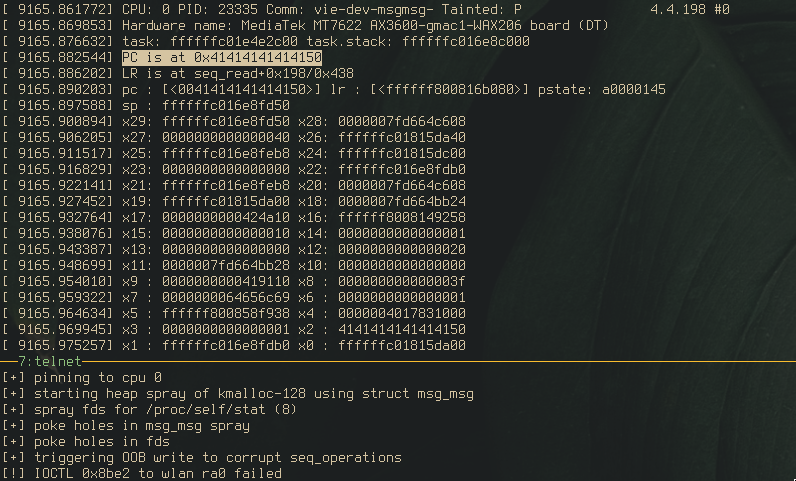
April 4, 2026 Iran Imposes New ‘Cash, Grass, Or Ass’ Fee For Strait Of Hormuz — The Onion (@theonion.com) April 03, 2026 kernel alchemy pt. 1: developing...
April 3, 2026
April 3, 2026 Iran Imposes New ‘Cash, Grass, Or Ass’ Fee For Strait Of Hormuz — The Onion (@theonion.com) April 03, 2026

April 3, 2026
April 3, 2026 ludocode/onramp (206 stars, C) A portable self-bootstrapping C compiler a C compiler in portable shell c89cc.sh - standalone C89/ELF64 compiler...

April 2, 2026
April 2, 2026 At [un]prompted, the illusion that vulnerability research won’t be automated away has passed. Specifically, it was Nicholas Carlini’s talk, a...
April 1, 2026
April 1, 2026 echidna and medusa fuzz smart contracts against properties you define. Complex state transitions, edge cases in arithmetic. Fuzzing finds what...

March 30, 2026
March 30, 2026 Excerpt from an unpublished article. https://t.co/hCeqz7YHlV pic.twitter.com/4mLAOSO2Ev— thaddeus e. grugq (@thegrugq) March 29, 2026 He said...