Is Anthropic’s Mythos genuinely “too powerful” to release, or is it just masterful marketing?
First up this week, Anthropic is making waves with its decision to withhold its new Claude Mythos model, claiming it is too powerful for public release. The move has drawn both scrutiny from the U.S. Treasury and skepticism from researchers who wonder if it's a marketing play to avoid technical oversight. Meanwhile, OpenAI revealed that a GitHub Actions workflow used to sign its macOS apps was compromised after it inadvertently downloaded a malicious library, though they report no internal systems were breached. We also look at a ransomware hit on North Sea energy infrastructure, the DRIFTR evasion technique that mimics human typing errors, and a critical vulnerability found in billions of devices by an AI researcher.
Anthropic said it had created an AI model so powerful that, out of a sense of overwhelming responsibility, it was not going to release it to the public. The US treasury secretary, Scott Bessent, summoned the heads of major banks for a chat about the model, Mythos. The model’s capacities were not “substantiated,” said Dr Heidy Khlaaf, the chief AI scientist at the AI Now Institute. “Releasing a marketing post with purposely vague language that obscures evidence … brings into question if they are trying to garner further investment without scrutiny.”
https://www.theguardian.com/technology/2026/apr/12/too-powerful-for-the-public-inside-anthropics-bid-to-win-the-ai-publicity-war
OpenAI revealed a GitHub Actions workflow used to sign its macOS apps, which downloaded the malicious Axios library on March 31, but noted that no user data or internal system was compromised.

OpenAI Revokes macOS App Certificate After Malicious Axios Supply Chain Incident
OpenAI revoked its macOS signing certificate after a malicious Axios dependency incident on March 31, 2026, preventing potential software misuse.
A major cybersecurity incident has shaken the offshore energy industry after Norwegian subsea engineering company K Subsea Group fell victim to a ransomware attack. The attack, attributed to the notorious Everest ransomware group, has led to encrypted systems and operational disruptions across key offshore projects in the North Sea. As one of the vital contributors to subsea infrastructure, the company’s temporary shutdown has sent ripples through both regional and global energy markets.
https://undercodenews.com/ransomware-shockwaves-hit-the-north-sea-inside-the-cyberattack-disrupting-global-energy-operations/
An evasion technique that is built to look like human error. DRIFTR is an adaptive behavioral obfuscation system that encodes intent through human-like error patterns and decodes it via probabilistic AI reconstruction. Designed to evade: casual observation, basic logging systems, keyword scanning.
https://anti-forensics.com/blog/driftr-behavioral-obfuscation-using-keyboard-drift-entropy-injection-and-ephemeral-decoding/
Attackers breached the website CPUID and replaced download links for CPU-Z and HWMonitor with malicious files for several hours. Users who downloaded them got infected with the STX RAT, giving attackers remote access to their systems. The short attack window still exposed many users to compromise.
https://securityaffairs.com/190702/malware/cpuid-watering-hole-attack-spreads-stx-rat-malware.html
Analysis of CISA's Known Exploited Vulnerabilities over the past four years shows critical vulnerabilities still open at Day 7 worsened from 56% to 63% despite teams closing 6.5x more tickets. Staffing cannot solve this. The problem is not speed. It is the operational model itself.
https://www.bleepingcomputer.com/news/security/analysis-of-one-billion-cisa-kev-remediation-records-exposes-limits-of-human-scale-security/
Hackers started exploiting a critical vulnerability in the Marimo open-source reactive Python notebook platform just 10 hours after its public disclosure. The flaw allows remote code execution without authentication in Marimo versions 0.20.4 and earlier. It tracked as CVE-2026-39987 and GitHub assessed it with a critical score of 9.3 out of 10. According to researchers at cloud-security company Sysdig, attackers created an exploit from the information in the developer's advisory and immediately started using it in attacks that exfiltrated sensitive information.
https://www.sysdig.com/blog/marimo-oss-python-notebook-rce-from-disclosure-to-exploitation-in-under-10-hours
A single hacker recently managed to compromise nine different Mexican government agencies by exploiting two popular AI platforms. This finding comes from the research firm Gambit Security, revealing that Claude Code, an AI-powered coding assistant, and OpenAI’s GPT-4.1 were used in the attack between December 2025 and February 2026.
https://hackread.com/hacker-claude-code-gpt-4-1-mexican-records/
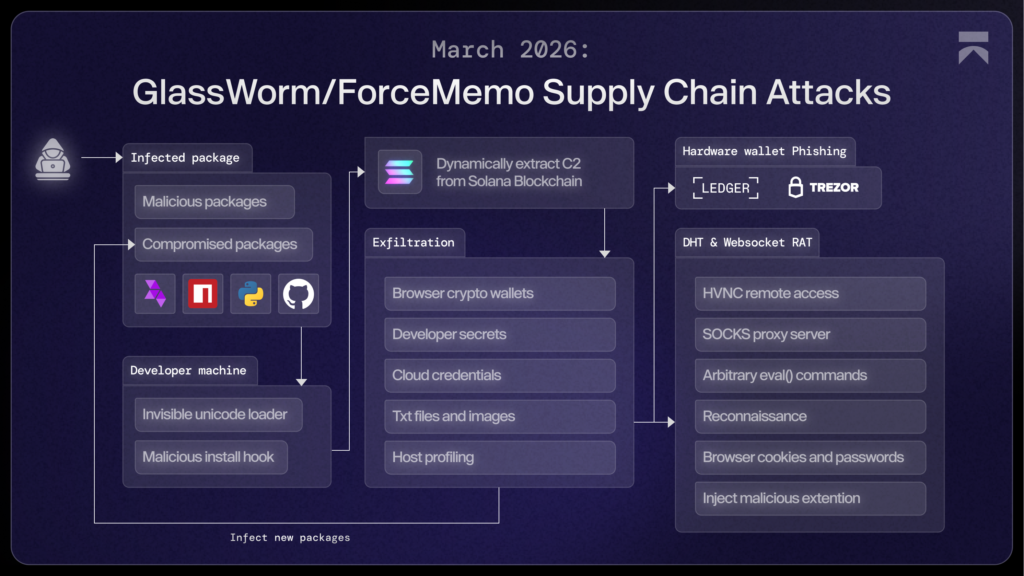
The GlassWorm campaign, active since 2025, has evolved from malicious npm packages to large-scale supply chain attacks across GitHub, npm, and VS Code, even deploying RATs via fake browser extensions. In its latest iteration, threat actors used a malicious OpenVSX extension impersonating WakaTime, bundling a Zig-compiled binary. Instead of acting as the payload, the binary serves as a stealthy dropper that infects multiple IDEs on a system, showing the group’s continuous adaptation.
GlassWorm evolves with Zig dropper to infect multiple developer tools
The GlassWorm campaign uses a Zig-based dropper hidden in a fake IDE extension to infect developer tools and compromise systems.
The FBI Atlanta Field Office and the Indonesian National Police have taken down a global phishing operation tied to more than $20 million in attempted fraud, according to authorities. The action included infrastructure seizures and the detention of a suspected developer linked to a widely used phishing kit.
https://hackread.com/fbi-atlanta-indonesian-police-w3llstore-phishing-market/
Thousands of Rockwell Automation’s Internet-exposed programmable logic controllers (PLCs) are among the attack surface targeted by hackers with ties to Iran in assaults targeting U.S. critical infrastructure networks. Iranian state-backed hacking organizations have been targeting Rockwell Automation/Allen-Bradley PLC equipment since March 2026, resulting in operational disruptions and financial losses, according to a joint alert released by several U.S. federal agencies on Tuesday.
https://www.reconbee.com/nearly-4000-us-industrial-devices-exposed-to-iranian-cyberattacks/
The cybercrime group Shiny Hunters is extorting Rockstar Games by publishing threats on their website. Rockstar Games has officially confirmed a cyber incident involving a cyberattack and data theft. The confirmation from Rockstar Games marks the first public acknowledgment of the security breach. No further impacts or mitigations were detailed in the available information.
https://www.cyberhub.blog/article/23759-rockstar-games-confirms-cyberattack-and-data-theft-by-shiny-hunters
A critical vulnerability (CVE-2026-5194) in the wolfSSL cryptographic library-used in billions of devices including VPNs, routers, automotive systems, power grids, and military applications-allows forged digital signatures to pass verification due to missing digest-size and OID checks. The flaw, rated CVSS 10.0 by Red Hat, was discovered by Anthropic researcher Nicholas Carlini using AI and could weaken ECDSA certificate-based authentication when certain conditions are met.
https://www.cve.org/CVERecord?id=CVE-2026-5194The FBI successfully extracted incoming Signal messages from a defendant's iPhone in a Texas terrorism case involving an alleged Antifa cell and an attack on an ICE detention facility.
Investigators accessed the messages from Apple's internal push notification database, where previews of incoming alerts remained stored despite the Signal app being deleted and disappearing messages used.
https://lifehacker.com/tech/fbi-extracted-deleted-signal-messages-from-a-defendants-iphone